
Navigating the Digital Frontier: Ensuring Safety on AIM
Understanding the Risks and Responsibilities
The digital landscape, while offering unprecedented connectivity, also presents a myriad of potential hazards. AIM, like any online platform, necessitates a cautious approach to safeguard personal information and maintain online security. In an era where data breaches and cyber threats are increasingly prevalent, understanding the fundamental principles of online safety is paramount. This isn't just about avoiding obvious scams; it's about cultivating a consistent, proactive stance against potential risks. It's akin to locking your doors at night – a simple, routine practice that provides a significant layer of security. We are, after all, dealing with a virtual world where the rules, while similar to the physical one, have their own unique complexities.
One of the initial steps in securing your AIM experience involves understanding the platform's security features. Familiarize yourself with privacy settings, account recovery options, and reporting mechanisms. Knowledge is your first line of defense. Consider it like learning the layout of a new city; you wouldn't wander aimlessly without a map, would you? Similarly, navigating AIM without understanding its security features is like venturing into the unknown. Digital safety isn't just about reacting to threats; it's about preempting them through informed practices. This proactive approach minimizes vulnerabilities and fosters a safer online environment.
Furthermore, maintaining strong, unique passwords for your AIM account and associated email addresses is crucial. Avoid easily guessable combinations and consider using a password manager to generate and store complex passwords. Think of your password as the digital equivalent of a sturdy lock; it should be robust and difficult to bypass. Regular password updates are also recommended, like changing the locks on your house periodically. This is not about paranoia; it's about prudent security practices. If one password is compromised, all related accounts can be vulnerable. The digital world has a way of reminding us that interconnectedness can be a double-edged sword.
Finally, be wary of unsolicited messages and links. Phishing attempts and malware distribution often occur through these channels. Exercise caution when interacting with unknown users and refrain from clicking on suspicious links. This is the digital equivalent of not accepting candy from strangers. Online, the 'candy' might be a malicious file or a link to a fraudulent website. Your digital intuition is your best first line of defense. If something seems too good to be true, it probably is. The internet is a vast place, and not everyone has your best interests at heart.
Protecting Your Personal Information on AIM
The Importance of Privacy and Discretion
Protecting personal information on AIM is a cornerstone of online safety. Avoid sharing sensitive details such as your full name, address, phone number, and financial information with unfamiliar users. Think of your personal data as precious jewels; you wouldn't leave them lying around for anyone to take, would you? The digital world requires the same level of vigilance. Sharing too much information can make you vulnerable to identity theft and other malicious activities. In essence, it's about maintaining a healthy level of digital discretion.
Be mindful of the information you share in your profile and status updates. Oversharing can provide valuable insights to potential attackers. Limit the visibility of your profile to trusted contacts and avoid posting details that could compromise your security. Consider your profile like the front window of your digital home; you wouldn't leave it wide open for everyone to see, would you? The digital world is often a public space, and what you post can be seen by a wider audience than you might anticipate. It is always wise to err on the side of caution.
When engaging in online conversations, be cautious about the information you disclose. Even seemingly innocuous details can be pieced together to form a comprehensive profile. Remember, online interactions can be easily recorded and shared. Think of your conversations as public speeches; anything you say can be used against you. Maintaining a level of anonymity and discretion is crucial. The internet has a long memory, and past actions can resurface unexpectedly.
Regularly review your privacy settings and ensure they align with your security preferences. AIM's privacy controls allow you to manage who can see your profile, contact you, and access your information. Treat your privacy settings like the locks on your digital doors; they need to be checked and updated regularly. As technology evolves, so do the methods used by cybercriminals. Staying informed and proactive is essential for maintaining a secure online presence. This is not about living in fear; it's about being prepared.
Recognizing and Avoiding Scams on AIM
Identifying Red Flags and Fraudulent Activities
Scams on AIM can take various forms, from phishing attempts to fraudulent offers. Recognizing the red flags is essential for avoiding these pitfalls. Be wary of messages that request personal information, financial assistance, or urgent action. Consider these requests like suspicious phone calls; you wouldn't give out your bank details to a stranger on the phone, would you? The same principle applies online. Scammers often rely on creating a sense of urgency or fear to manipulate their victims.
Pay attention to the language and grammar used in messages. Scammers often make grammatical errors and use generic greetings. These are like the telltale signs of a counterfeit product; they lack the polish and professionalism of legitimate communications. Trust your instincts; if a message seems suspicious, it probably is. The digital world, like the physical one, has its share of con artists.
Verify the authenticity of any offers or promotions received through AIM. Scammers often use fake accounts to impersonate legitimate organizations or individuals. Always double-check information through official channels. Think of it as verifying the credentials of a salesperson; you wouldn't buy something from someone without checking their credentials, would you? The internet offers a wealth of information; use it to your advantage. A little research can go a long way in preventing fraud.
Report any suspicious activity or scams to AIM's support team. By reporting these incidents, you contribute to a safer online environment for everyone. Consider it like reporting a crime to the police; it helps protect others from becoming victims. Collective vigilance is essential for combating online scams. The digital world is a community, and we all have a role to play in keeping it safe.
Maintaining Account Security on AIM
Best Practices for Long-Term Protection
Maintaining account security on AIM is an ongoing process that requires consistent effort. Enable two-factor authentication (2FA) whenever possible. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone. Think of 2FA as a double lock on your digital door; it makes it much harder for unauthorized individuals to gain access. In the digital age, redundancy is your friend.
Regularly update your AIM software and operating system. Software updates often include security patches that address known vulnerabilities. Keeping your software up-to-date is like regularly servicing your car; it ensures optimal performance and prevents potential breakdowns. The digital world is constantly evolving, and so are the threats. Staying current is essential for maintaining security. Software developers are always working to improve security; take advantage of their efforts.
Be cautious when using public Wi-Fi networks. Avoid accessing sensitive information, such as your AIM account, on unsecured networks. Public Wi-Fi networks are often vulnerable to eavesdropping and data interception. Consider public Wi-Fi like a public phone booth; you wouldn't discuss sensitive information in a public place, would you? Using a virtual private network (VPN) can add an extra layer of security when using public Wi-Fi. It's like having a private conversation in a crowded room.
Monitor your account activity for any suspicious behavior. Regularly check your login history and account settings for unauthorized changes. Early detection is crucial for minimizing the impact of potential security breaches. Think of it as checking your bank statements for unauthorized transactions; you need to be vigilant and proactive. The digital world requires constant awareness; a moment of inattention can lead to significant consequences.
Staying Informed and Educated About AIM Security
Continuous Learning for Enhanced Safety
Staying informed about the latest security threats and best practices is crucial for maintaining a safe AIM experience. Follow reputable security blogs and news sources to stay updated on emerging threats. Consider it like staying informed about weather patterns; you need to be aware of potential storms to prepare accordingly. The digital world is constantly changing, and so are the threats. Continuous learning is essential for maintaining security. Knowledge is power, especially in the digital realm.
Participate in online security forums and communities. Sharing experiences and knowledge with others can help you stay informed and learn from others' mistakes. Think of it as joining a neighborhood watch; collective vigilance is more effective than individual efforts. The digital world is a community, and we all have a responsibility to contribute to its safety. Sharing information can help others avoid common pitfalls.
Educate yourself about common social engineering tactics. Scammers often use manipulation and deception to trick users into revealing personal information. Understanding these tactics can help you recognize and avoid them. Consider it like learning about common scams; you need to be aware of the tricks to avoid falling for them. The digital world is full of illusionists; don't let them deceive you.
Regularly review AIM's terms of service and privacy policies. These documents contain important information about your rights and responsibilities as a user. Staying informed about these policies can help you understand how your data is collected and used. Think of it as reading
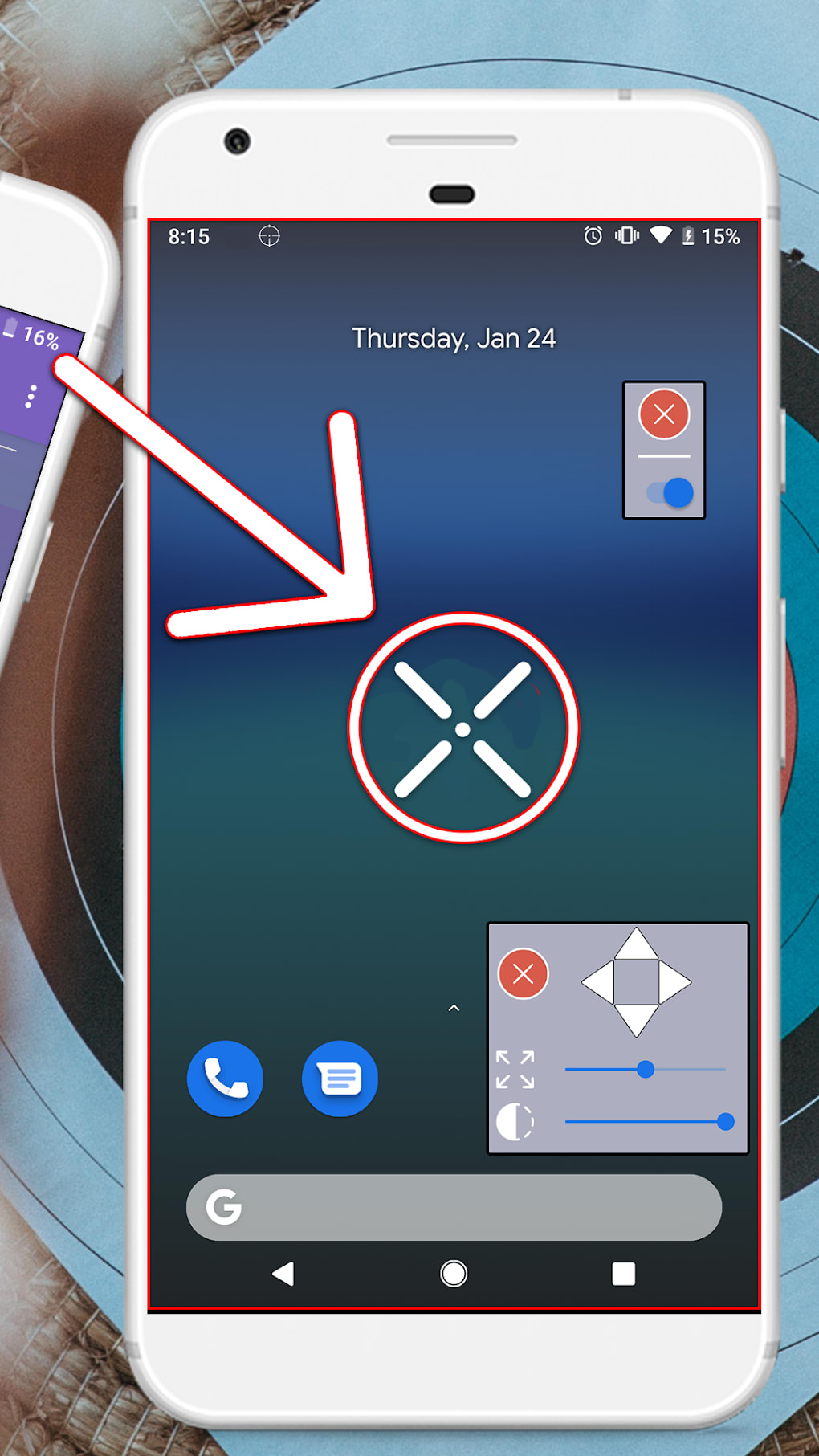
Crosshair Custom Aim Safe For Android Download

Aim Safe Needle Recapper, Stick Protector, 4/pk Clinaide

Septodont Aim Safe Needle Recapper, 4/pk Supply Clinic
Safe Aim Stocks 2 Bottom Up Iht Planning Share Talk
![safe aim [banned] youtube safe aim [banned] youtube](https://i.ytimg.com/vi/mDvY-06uJe4/maxresdefault.jpg)


No comments:
Post a Comment